Why Identity Security Matters More Than Ever
An automated id verification system uses artificial intelligence and biometric technology to instantly confirm someone’s identity by scanning government-issued documents, comparing facial features, and checking multiple databases without human intervention.
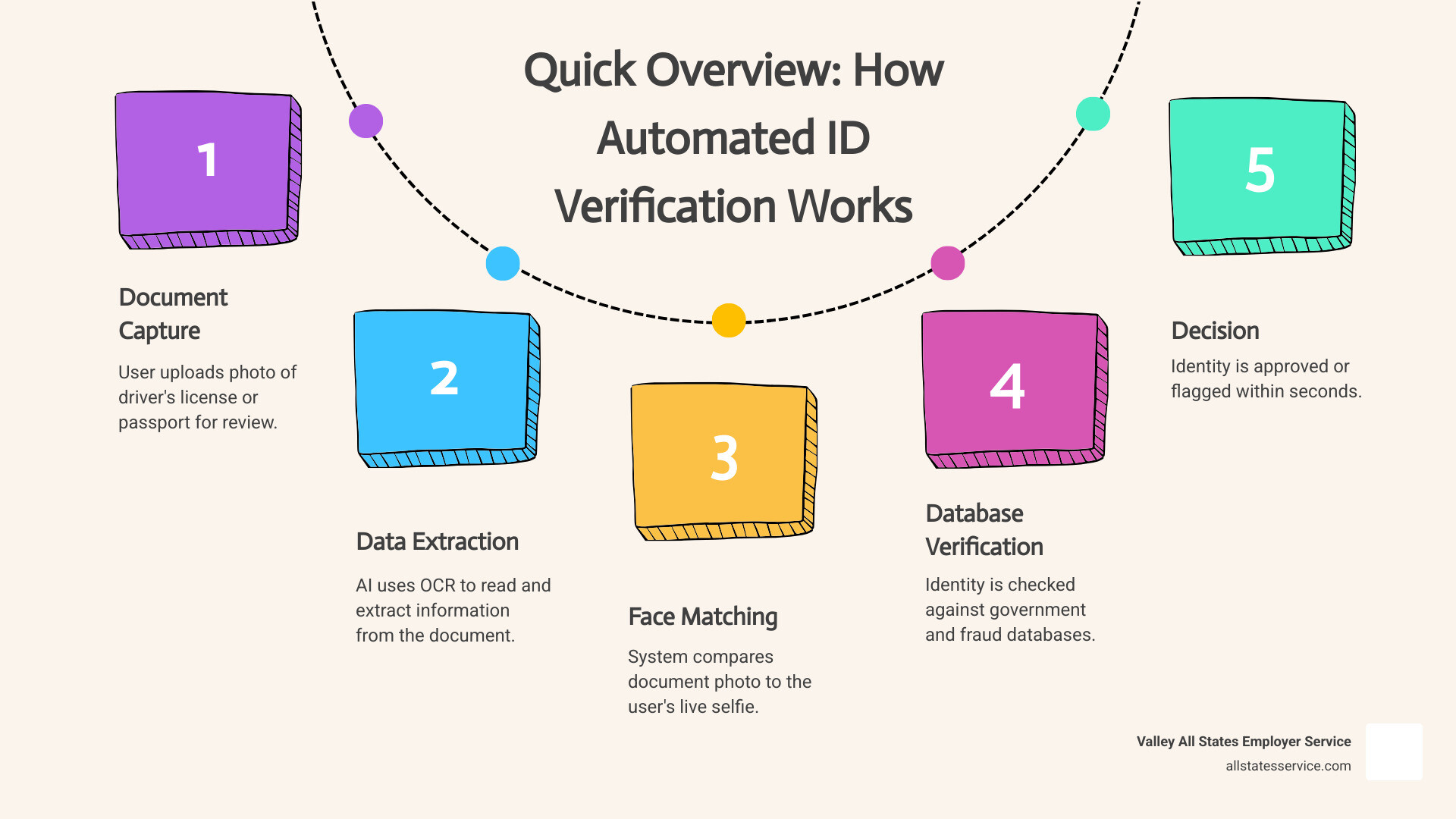
Quick Overview: How Automated ID Verification Works
- Document Capture – User uploads photo of driver’s license or passport
- Data Extraction – AI reads and extracts information using Optical Character Recognition
- Face Matching – System compares document photo to user’s live selfie
- Database Verification – Checks identity against government and fraud databases
- Decision – Approves or flags identity within seconds
Think about the last time you took a selfie to verify your identity for a bank app or job application. That simple action triggered a sophisticated system working behind the scenes.
As an HR manager, you’re constantly balancing speed with accuracy during onboarding. Every new hire needs verification, but manual document checks eat up valuable time and leave room for human error. Meanwhile, identity fraud keeps getting more sophisticated.
The shift to remote work made things even more complicated. How do you verify someone’s identity when they’re not physically in your office? How do you ensure compliance with regulations like I-9 requirements when everything happens digitally?
Automated systems handle these challenges by combining speed, accuracy, and security in ways manual processes simply can’t match. They work 24/7, process verifications in seconds rather than days, and catch fraudulent documents that might fool the human eye.
But like any technology, these systems come with their own questions. How accurate are they really? What about privacy concerns? How do you choose the right solution when dozens of vendors promise the same results?
+automated +id +verification +system word roundup:
Understanding the Automated ID Verification System
What exactly is an automated id verification system, and why is it becoming so crucial for businesses across the United States, including those in Maryland and Lutherville MD? At its core, it’s a technology-driven solution designed to confirm a person’s identity quickly and reliably without requiring a human to manually review documents or cross-reference databases. This process, often called identity proofing, is vital in today’s digital world.
Imagine a secure digital vault where all your identity checks happen instantly. That’s essentially what an automated system provides. It uses advanced technologies like artificial intelligence (AI), machine learning (ML), and biometric data analysis to scrutinize identity documents and verify the legitimacy of the person presenting them. This helps businesses comply with regulations, prevent fraud, and build trust with their customers and employees.
For employers, this translates directly to efficiency in processes like employee onboarding. Instead of spending hours manually checking I-9 forms and other identity documents, an automated eligibility verification system can handle much of the heavy lifting. This allows HR teams to focus on more strategic tasks, knowing that crucial compliance steps are being managed effectively.
How an Automated ID Verification System Works
Let’s break down the mechanics of how an automated id verification system performs its magic. The process typically begins with the user capturing an image of their government-issued ID, like a driver’s license or passport, using a smartphone or webcam.
- Document Capture and Data Extraction: Once the image is submitted, the system employs Optical Character Recognition (OCR) technology. OCR scans the document and extracts key information, such as name, date of birth, document number, and expiry date. It’s like having a super-fast, super-accurate data entry clerk that never makes a mistake.
- Document Authenticity Checks: The system then performs a series of sophisticated checks on the document itself. It looks for visual cues of tampering, such as altered fonts, mismatched holograms, or signs of physical manipulation. It can also verify security features like watermarks and microprinting.
- Face Matching and Liveness Detection: To ensure the person submitting the ID is the legitimate owner, the system often asks for a live selfie or a short video. AI algorithms compare this live image to the photograph on the ID document. Crucially, it also uses liveness detection to confirm that the person is real and not a spoof (like a photo or video playback). This helps prevent identity theft and ensures the person is physically present during the verification.
- Database Verification: Finally, the extracted data and verified identity are cross-referenced against various reputable databases. These might include government watchlists, fraud databases, and public records. This step helps confirm the identity’s validity and flags any suspicious activity or inconsistencies.
For employment-related verifications, this streamlined process is invaluable. Imagine the time saved with Automated I-9 Verification, ensuring compliance for every new hire efficiently and accurately.
Different Types of Automated ID Verification System Solutions
The world of automated ID verification is diverse, offering various solutions custom to different needs and risk levels. Understanding these types helps businesses choose the right tools for their specific challenges.
- Document Verification: This is perhaps the most common type, focusing on authenticating government-issued identity documents. Systems analyze features like holograms, watermarks, fonts, and machine-readable zones (MRZ) to detect counterfeits or alterations.
- Biometric Identification: Moving beyond just documents, biometric systems verify identity using unique biological characteristics. This can include facial recognition, fingerprint scanning, or even voice recognition.
- Database Checks: These systems verify identity by cross-referencing provided information (name, address, date of birth) against extensive public and private databases. This helps confirm the existence and legitimacy of an individual’s identity, often used in conjunction with document and biometric checks for a more comprehensive verification.
- Knowledge-Based Authentication (KBA): While less common in purely automated systems, KBA involves asking users questions based on their personal history that only they should know. This can be integrated into automated flows as a secondary verification method.
- Hybrid Solutions: Many modern automated systems combine several of the above methods to create a multi-layered approach. For example, a system might perform document verification, followed by a live facial scan, and then a database check. This layered security provides the highest level of assurance.
For employers, especially those navigating federal requirements, understanding these types is crucial. Solutions like the E-Verify Program Complete Guide offer specific guidance on employment eligibility verification, often leveraging these automated methods.
If you want help applying these verification steps to hiring workflows without adding more admin work, you can also explore our Automated Eligibility Verification System.
Key Features and Fraud Prevention Tactics
How does an automated id verification system manage to be so accurate and effective at preventing fraud? It’s about the fraud defenses built into modern verification flows, designed to spot both obvious fakes and more subtle manipulation.
One critical feature is liveness detection. This technology helps confirm the person interacting with the system is a real, live individual and not a static image, a video playback, or a sophisticated mask. This is a powerful anti-spoofing measure. Techniques range from asking the user to blink or turn their head, to analyzing subtle movements and skin texture. The goal is simple, reduce the risk that someone can verify an identity without being physically present.
Another important aspect is the continuous refinement of AI algorithms. These systems learn from new fraud patterns and evolve their detection capabilities over time. For employers managing sensitive hiring workflows, these features can act as an early warning system before a bad actor makes it into your process. This becomes especially important when you’re managing your Workforce Eligibility Verification at scale.
Ensuring Accuracy Through AI
The accuracy of an automated id verification system comes from its reliance on artificial intelligence and machine learning. These technologies help systems process large volumes of checks consistently and spot patterns that are hard to catch in manual review.
- Machine Learning (ML): ML models can be trained on large datasets of legitimate and fraudulent documents and biometric samples. Over time, they learn to recognize anomalies that may signal tampering or impersonation.
- Pattern Recognition: AI can compare a submitted ID against a library of known document templates, checking for consistency in layout, fonts, and security features. For face matching, it maps facial landmarks and compares them with the document photo while accounting for common differences like lighting and minor appearance changes.
- Fraud Detection Signals: Some systems can flag behavior patterns, repeated attempts, or mismatches that suggest higher risk. Used correctly, this reduces the chance of onboarding a fraudulent employee or approving a bad account.
For businesses, this can mean fewer errors and less manual rework. Our Automated Employment Verification Ultimate Guide digs deeper into how automation supports a more secure hiring process.
Automated Verification in Technical Workflows
Automated verification principles show up outside of HR too. In software development, tools like Gerrit Code Review use automated checks to maintain integrity and track changes.
In these systems, a unique “Change-Id” tag is often inserted into commit messages. That tag helps track code changes across development stages, including after cherry-picking or rebasing. Gerrit can also enforce rules like --require-change-id, ensuring submissions follow consistent tracking.
Access controls are also automated, defining who can push, review, and merge changes. Labels like “Code-Review” and “Verified” can be required before code is accepted. The idea is the same as identity verification, set clear rules, verify against them consistently, and keep an audit trail.
That same mindset matters for employment documentation. If you’re modernizing I-9 workflows, an auditable digital process can help reduce errors and support compliance. See our Electronic I-9 Solution Guide 2026 for practical details.
Navigating Legal Compliance and Regulatory Standards
Implementing an automated id verification system isn’t just about technology; it’s also about navigating a complex landscape of legal and regulatory requirements. Businesses, especially those operating in the United States, must adhere to various laws designed to protect consumer data and prevent financial crime.
Key regulations include:
- GDPR (General Data Protection Regulation): While primarily a European Union regulation, GDPR’s broad reach means it can apply to any U.S. business that processes personal data of EU citizens. It mandates strict rules for data collection, storage, and processing, emphasizing consent, data minimization, and the right to be forgotten.
- CCPA (California Consumer Privacy Act): This U.S. state-level law provides California consumers with significant rights regarding their personal information, including the right to know what data is collected, to delete it, and to opt out of its sale. Similar laws are emerging in other states.
- AML (Anti-Money Laundering) and KYC (Know Your Customer) Regulations: Financial institutions, in particular, are subject to stringent AML and KYC laws that require them to verify the identity of their customers to prevent illicit financial activities. Automated ID verification plays a crucial role in meeting these obligations efficiently.
- State-Specific Requirements: Beyond federal and international laws, states may have their own identity verification mandates. For instance, in Maryland, there are specific instructions for identity verification, such as those provided for unemployment insurance claims, which might involve systems like TrueID Identity Verification Instructions.
The core challenge revolves around data privacy. Automated systems handle sensitive personal information, so ensuring robust data security, transparent data handling practices, and compliance with these regulations is paramount. Ignoring these aspects can lead to hefty fines and reputational damage. For comprehensive guidance on compliance, particularly for I-9 forms, refer to our I-9 Compliance Services Complete Guide.
Benefits for Modern Businesses
The adoption of an automated id verification system brings a wealth of benefits for modern businesses, changing how they operate and interact with customers and employees.
- Operational Efficiency: Perhaps the most immediate benefit is the dramatic increase in efficiency. Manual identity checks are time-consuming and labor-intensive. Automated systems complete verifications in seconds, drastically reducing processing times. This means faster onboarding for new hires, quicker customer sign-ups, and streamlined compliance workflows.
- Improved User Experience: Users expect instant gratification. A seamless, fast, and user-friendly verification process contributes significantly to a positive customer and employee experience. It reduces friction, minimizes abandonment rates, and builds trust.
- Fraud Prevention: Automated systems are far more effective at detecting sophisticated fraud than human reviewers. Their ability to analyze multiple data points, perform liveness detection, and cross-reference databases in real-time provides a powerful defense against identity theft, synthetic identity fraud, and document forgery.
- Cost Reduction: By automating a previously manual process, businesses can significantly cut down on operational costs associated with staffing, training, and potential errors. The reduction in fraud losses also contributes to overall cost savings.
- Improved Compliance: Staying compliant with complex regulations like KYC, AML, and I-9 requirements is a heavy burden. Automated systems provide a consistent, auditable, and reliable method for meeting these obligations, reducing the risk of penalties. This is particularly valuable for E-Verify for Small Businesses, which might have limited resources for compliance.
Potential Challenges and Drawbacks
While the advantages of an automated id verification system are clear, it’s also important to acknowledge the potential drawbacks and challenges businesses might face during implementation and ongoing use.
- Technical Integration: Integrating a new automated ID verification system with existing business processes and IT infrastructure can be complex. It requires careful planning, technical expertise, and potentially significant development work to ensure seamless operation with current HR systems, customer relationship management (CRM) platforms, or other core applications.
- False Negatives and Positives: No system is 100% perfect. Automated systems can sometimes produce “false negatives” (rejecting a legitimate user) or “false positives” (approving a fraudulent one). While AI continuously improves, these errors can lead to frustrated users or, worse, successful fraud attempts. Striking the right balance between security and user experience is a delicate act.
- Privacy Concerns: Despite their security benefits, automated systems handle highly sensitive personal data. This raises legitimate privacy concerns among users and requires businesses to be transparent about how data is collected, stored, and used. Ensuring compliance with regulations like GDPR and CCPA is crucial, as is maintaining robust data security measures to prevent breaches.
- Cost of Implementation and Maintenance: While automated systems can reduce long-term operational costs, the initial investment in software, integration, and ongoing maintenance can be substantial, especially for smaller businesses.
- Bias in Algorithms: AI algorithms, if not properly trained and monitored, can sometimes exhibit biases present in their training data. This could lead to disproportionate rejection rates for certain demographic groups, raising ethical concerns and potentially legal challenges.
These challenges highlight the importance of careful vendor selection and a thoughtful implementation strategy. For example, when dealing with remote employees, navigating Remote I-9 Compliance requires a system that minimizes false negatives while maintaining strict security.
Choosing the Right Solution for Your Business
Selecting the ideal automated id verification system for your business is a critical decision that impacts efficiency, security, and compliance. With numerous providers offering various features, how do you make an informed choice?
Start by assessing your specific needs. What kind of identities do you need to verify? What volume of verifications do you anticipate? What are your industry’s specific regulatory requirements?
Here are key factors to consider:
- Accuracy and Fraud Detection Capabilities: Look for systems with high accuracy rates, robust liveness detection, and advanced fraud detection algorithms. Ask about their false positive and false negative rates.
- Document Coverage: Does the system support the range of identity documents you expect to encounter, both domestically and internationally (if applicable)?
- Scalability: Can the system handle your current verification volume, and can it scale easily as your business grows?
- API Integration: Seamless integration with your existing HR, CRM, or other business software is crucial. A strong API (Application Programming Interface) makes this process much smoother.
- User Experience: The verification process should be intuitive and quick for your users to minimize drop-off rates.
- Compliance and Data Privacy: Ensure the vendor adheres to all relevant data protection laws (e.g., GDPR, CCPA, local Maryland regulations) and has strong data security protocols.
- Customer Support: Reliable technical support and guidance are invaluable, especially during implementation and in case of issues.
- Cost-Effectiveness: Compare pricing models and ensure the solution offers good value for your investment, considering both initial setup and ongoing usage.
Many businesses find value in E-Verify Outsourcing because it taps into expert solutions without the burden of in-house management. This allows them to focus on their core operations while ensuring compliance.
Integration with Existing Processes
A truly effective automated id verification system doesn’t just exist in a silo; it integrates seamlessly into your existing business processes, enhancing rather than disrupting them. The goal is to achieve workflow automation that simplifies operations and improves efficiency.
For HR departments, this means integrating with your existing HR software or applicant tracking systems. When a new hire is onboarded, the system can automatically trigger the identity verification process, pulling necessary data and feeding results back into your HR platform. This creates a more Streamline Onboarding Process Complete Guide, reducing manual data entry, minimizing errors, and ensuring compliance from day one.
For customer-facing businesses, integration means connecting with your customer onboarding platforms or CRM systems. When a new customer signs up, their identity can be verified instantly, allowing for immediate account activation or service provision. This not only speeds up the process but also provides a consistent and secure experience.
Key aspects of successful integration include:
- API-First Design: Look for solutions built with robust APIs that allow for flexible and customizable connections to your various systems.
- Configurable Workflows: The system should allow you to configure verification flows that match your specific business logic and compliance requirements.
- Data Synchronization: Ensure that data can flow securely and accurately between the verification system and your other platforms, avoiding data silos and manual reconciliation.
- Reporting and Auditing: Integrated systems should provide comprehensive reports and audit trails, making it easy to track verification statuses and demonstrate compliance.
By carefully planning integration, businesses can open up the full potential of an automated id verification system, changing it into a powerful tool that drives efficiency, security, and compliance across their operations.
Frequently Asked Questions
What is the difference between manual and automated ID verification?
The primary difference lies in human involvement and speed. Manual ID verification relies on a person to physically examine documents, compare photos, and cross-reference information. This process is often slow, prone to human error, and less effective at detecting sophisticated fakes. An automated id verification system, on the other hand, uses AI, machine learning, and biometrics to perform these checks digitally and instantly. It’s faster, more accurate, available 24/7, and far superior at identifying fraudulent documents or spoofing attempts.
Is automated ID verification safe for user data?
When implemented correctly by reputable vendors, automated ID verification systems are designed with high-level security measures to protect user data. They typically employ encryption for data in transit and at rest, secure data storage practices, and strict access controls. However, the safety of user data also depends on the business using the system to comply with data privacy regulations like GDPR and CCPA, ensuring transparent data handling, obtaining proper consent, and having robust internal security policies. Choosing a trusted provider with strong security certifications is essential.
How long does the automated verification process take?
One of the greatest advantages of an automated id verification system is its speed. While manual verification can take minutes, hours, or even days, automated processes typically complete identity checks in a matter of seconds. After a user uploads their document and potentially a live selfie, the AI algorithms can extract data, perform authenticity checks, conduct face matching, and run database queries almost instantaneously. This rapid turnaround significantly improves user experience and operational efficiency for businesses.
Conclusion
We’ve explored the intricate world of the automated id verification system, from its fundamental workings to its profound impact on modern business. This technology is more than just a convenience; it’s a critical tool for navigating the complexities of digital identity, fraud prevention, and regulatory compliance in the United States, including our local Maryland communities.
We’ve seen how AI and machine learning power these systems, enabling them to verify identities with unprecedented speed and accuracy, far beyond what manual processes can achieve. The benefits are clear: increased operational efficiency, improved user experience, robust fraud prevention, and seamless compliance with vital regulations like I-9 requirements. While challenges like integration and privacy concerns exist, careful planning and vendor selection can mitigate these risks.
Looking ahead, the future of automated ID verification technology is bright and dynamic. We anticipate even more sophisticated biometric methods, including behavioral biometrics, and the integration of emerging technologies like blockchain for immutable identity records. As digital interactions become more prevalent, these systems will continue to evolve, offering even greater security and efficiency.
At Valley All States Employer Service, we understand the complexities of employment compliance, especially when it comes to verifying the eligibility of your workforce. Our expertise in E-Verify and I-9 compliance means we’re constantly working to provide solutions that leverage the best of automated verification, reducing your administrative burden and ensuring you meet all federal and state requirements. We empower businesses to focus on growth, knowing their compliance needs are expertly handled.
Ready to simplify your compliance? Explore our automated eligibility verification system today.
